A threat actor has allegedly exfiltrated approximately 100 GB of personally identifiable information (PII) from Crunchyroll, the Sony-owned anime streaming platform, after gaining access through a compromised employee at its outsourcing partner, Telus.
The breach is reported to have occurred on March 12, 2026, but has not been publicly acknowledged by Crunchyroll at the time of publication.
According to the threat actor, who contacted Cyber Digest, the intrusion began when an employee at Telus, which provides business process outsourcing (BPO) services to Crunchyroll, executed malware on their workstation. This allowed the attacker to gain initial access and establish a foothold within Crunchyroll’s internal environment.
From there, the attacker claims to have moved laterally into sensitive systems, including customer-facing infrastructure such as the company’s ticketing platform.
The method of attack is consistent with a broader pattern observed in the Telus Digital incident, also dated March 12, 2026, in which threat actors claimed to have accessed data from Telus and several companies that rely on its BPO services, including customer support, AI data operations, and content moderation.
Because BPO providers often manage authentication and billing systems across multiple clients, they are considered high-value targets for threat actors seeking to maximize impact through a single breach.
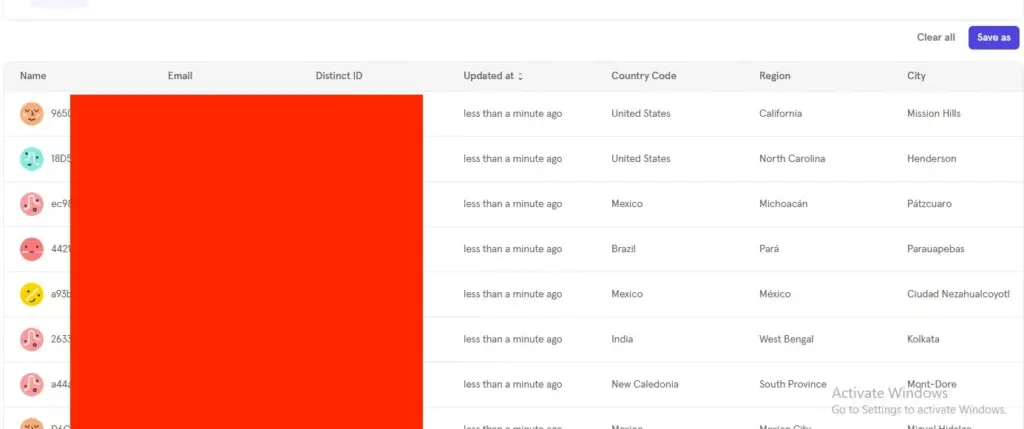
Cyber Digest reported that it analyzed a sample of the allegedly stolen data provided by the threat actor. The sample reportedly included sensitive user information such as IP addresses, email addresses, credit card details, and customer analytics data containing PII.
The threat actor claims that a total of 100 GB of data was extracted from Crunchyroll’s customer analytics environment and ticketing systems. If confirmed, the exposure could pose significant risks, including identity theft, financial fraud, and targeted phishing attacks against users.
The attacker further stated that Crunchyroll detected the intrusion and revoked access approximately 24 hours after the initial breach. Despite the limited access window, the scale of the data exfiltration suggests the operation may have been pre-planned and executed rapidly.
The threat actor also alleged that Crunchyroll has not responded to any communications regarding the breach and has not issued any public disclosure to affected users.
The situation raises additional concerns as Crunchyroll was already facing a class-action lawsuit earlier in 2026 over allegations of sharing user viewing data with third-party marketing platforms without proper consent.
Crunchyroll has not responded to requests for comment as of publication. The situation remains ongoing.
Source: Cybersecurity News